Proactive Cybersecurity That Shields Your Digital World
Detect, deter, and respond to threats with tailored security operations, giving you peace of mind.
Founded by former security engineers, we built a practical, hands on approach to defending mid market to enterprise clients. We blend risk assessment, zero trust architecture, and continuous monitoring to reduce dwell time and prevent breaches. Our team emphasizes transparency, measurable outcomes, and ongoing collaboration to adapt to evolving threats.
What We Deliver
Threat Assessment & Gap Analysis
Comprehensive evaluation of security gaps, data flows, and control effectiveness to prioritize remediation and strengthen security posture.

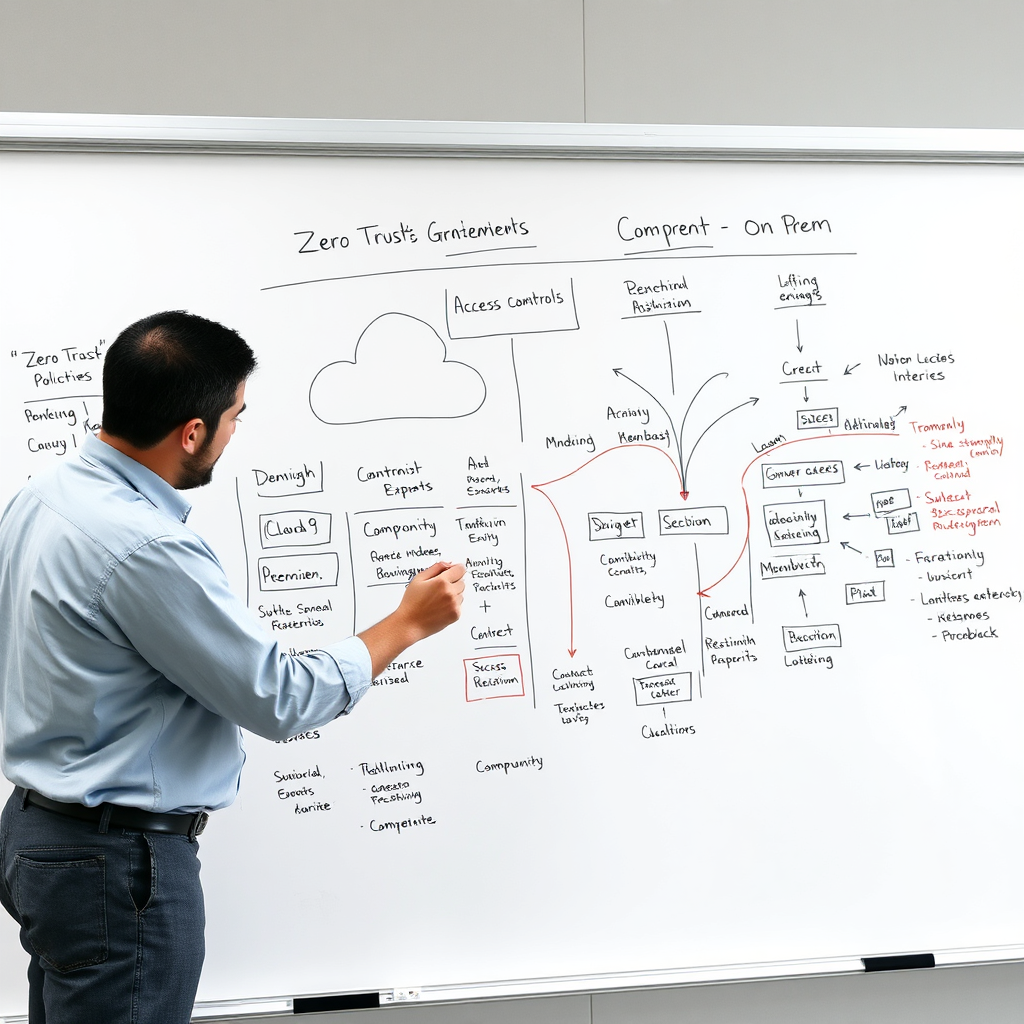
Zero Trust Architecture Design
Design and implement identity centric controls, micro segmentation, and continuous verification to reduce breach risk across cloud and on premise.
Managed Detection & Response
Continuous monitoring, threat detection, and rapid containment with expert guided remediation and ongoing improvement.

Cybersecurity Solutions for a Safer Digital World

Automated Threat Hunting
Leverages AI driven analytics to continuously search endpoints and networks for subtle indicators of compromise, reducing dwell time and enabling faster containment. By correlating threat intel with behavioral baselines, it uncovers stealthy activity traditional tools miss. This approach also reduces false positives and improves response confidence for security teams.

Zero Trust by Default
Design and implement identity centric controls, strict access policies, micro segmentation, and continuous verification to minimize attack surfaces across cloud and on prem environments.

Incident Response Playbooks
Modular, role based playbooks guide your team from detection through remediation, with drill based validation, clear comms plans, and rapid containment to minimize business impact.
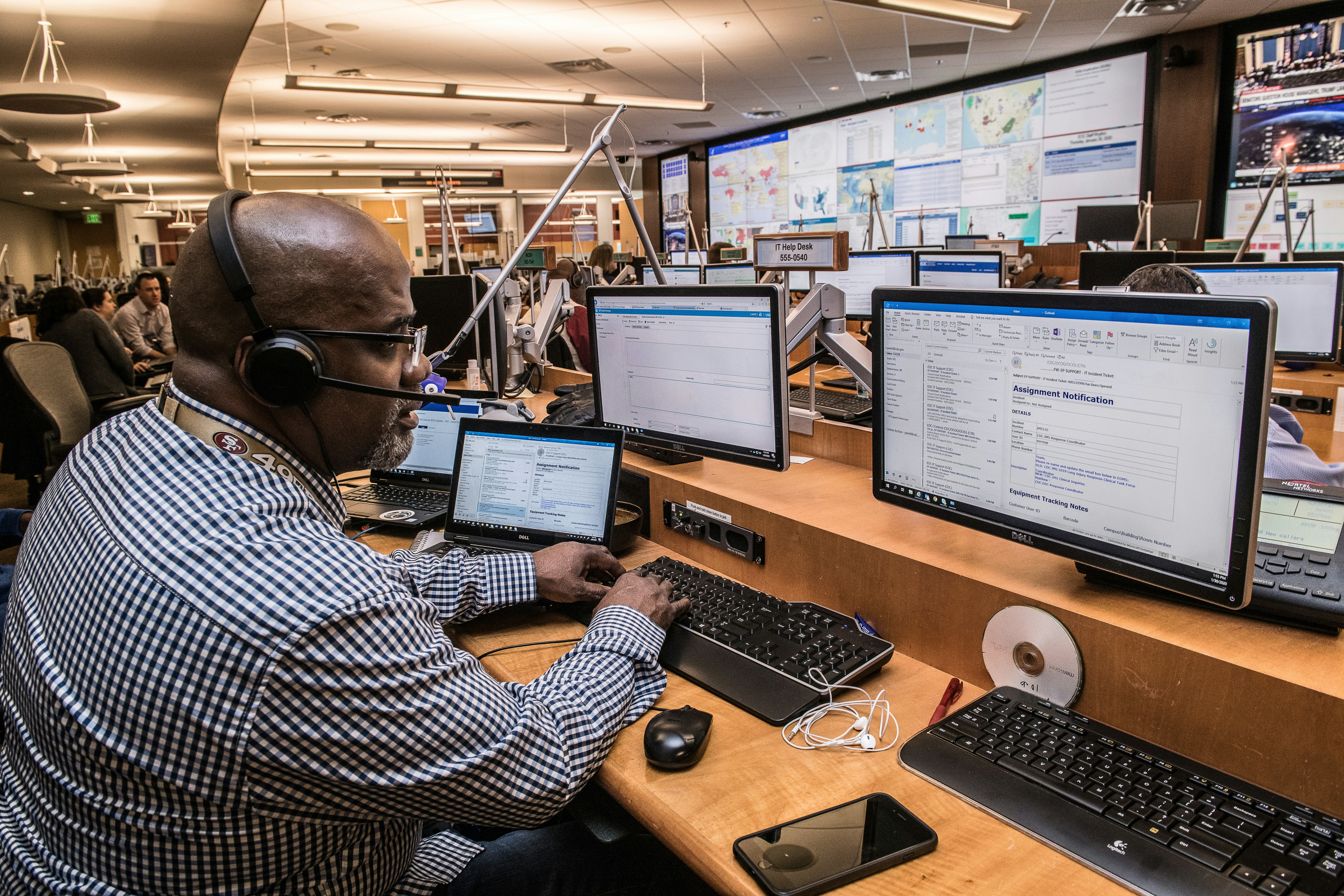
24/7 Threat Detection, Incident Response, and Compliance
Around-the-Clock Monitoring
Around-the-clock monitoring across endpoints, networks, and cloud services with triage workflows, escalating high severity alerts to the right experts for rapid containment and transparent updates. We supplement with threat intelligence feeds and security analytics to improve context and prioritization for better decision making during incidents.


Rapid Incident Response
Pre defined, collaborative response playbooks align IT, security, and legal teams to contain threats quickly, preserve evidence, and restore services with clear stakeholder communication. We test and refine these playbooks through regular simulations, ensuring rapid escalation, accurate forensics, and documented lessons learned that strengthen future responses.
Compliance Readiness
Map controls to ISO 27001, SOC 2, HIPAA or relevant standards and deliver audit ready reports, evidence packs, and ongoing governance to reduce regulatory risk. Our approach includes continuous alignment with frameworks and automated evidence collection to simplify audits and demonstrate due care to customers.

Security Assessments, Custom Roadmaps, and Proactive Protection
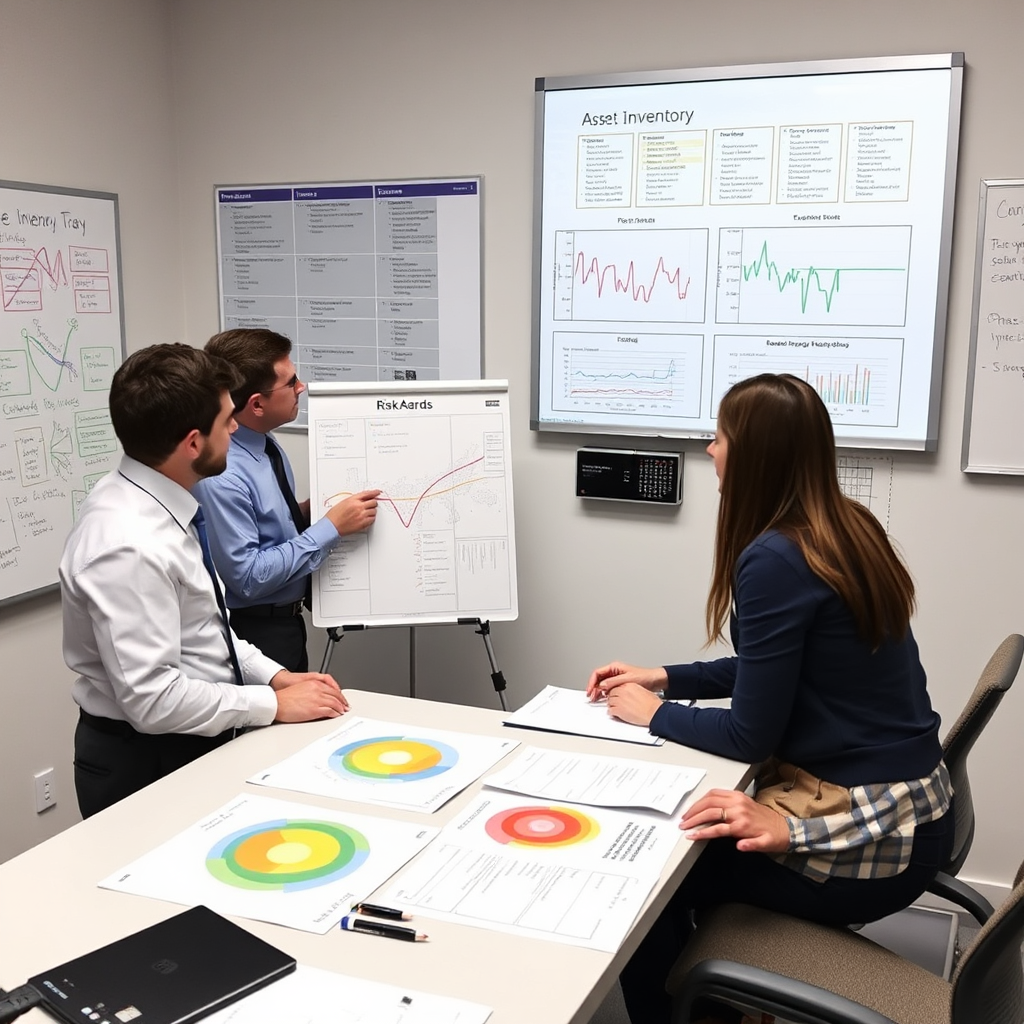
Comprehensive Risk Assessments
Asset inventories, threat modeling, and risk scoring that translate into prioritized remediation and measurable security improvements. By quantifying impact and likelihood, we help leadership allocate resources effectively and track progress over time. This disciplined approach reduces surprises and aligns security with business goals.

Tailored Roadmaps
Turn findings into a practical roadmap with phased milestones, owners, and measurable outcomes. We tailor timelines to your resources, integrate with existing teams, define clear success metrics, and provide executive ready summaries to secure alignment and funding while staying adaptable to changing threats.

Proactive Defenses
Implement proactive controls such as automated patching, secure configurations, continuous monitoring, and regular table top exercises to close gaps before attackers exploit them, delivering stronger resilience and lower incident costs. We validate defenses through tabletop exercises and purple team activities to ensure practical effectiveness and quick recovery times.